NIST is overhauling how it manages the National Vulnerability Database (NVD) and switching to a risk-based model that prioritizes “enrichment” of only the most critical CVE-numbered security vulnerabilities.
“This change is driven by a surge in CVE submissions, which increased 263% between 2020 and 2025,” the National Institute of Standards and Technology said. “We don’t expect this trend to let up anytime soon.”

A two-year struggle and a new approach
NIST has been struggling to update NVD’s CVE entries with relevant information – descriptions, severity (CVSS) scores, known affected software configurations, etc. – for over two years.
The problem was acknowledged in early 2024 and despite occasional optimistic updates, it’s now become clear that the veritable onslaught of CVE-numbered security issues is too much for NVD’s analysts to tackle.
“We are working faster than ever. We enriched nearly 42,000 CVEs in 2025 — 45% more than any prior year. But this increased productivity is not enough to keep up with growing submissions. Therefore, we are instituting a new approach,” NIST announced.
“All submitted CVEs will still be added to the NVD. However, those that do not meet the criteria above will be categorized as ‘Not Scheduled.’ This will allow us to focus on CVEs with the greatest potential for widespread impact.”
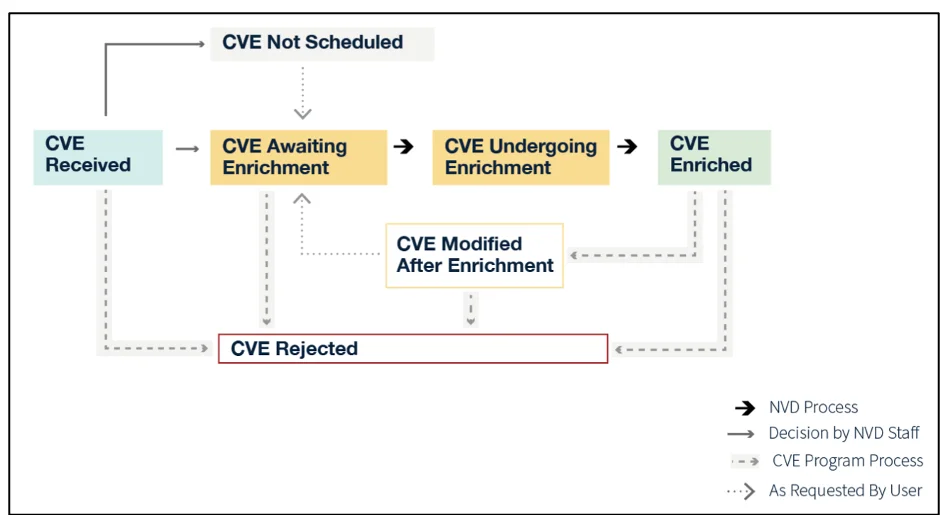
The new NVD CVE processing workflow (Source: NIST)
From now on, the CVE entries that will be prioritized for enrichment will fall into one of three categories:
- They’ve already been added to the Cybersecurity and Infrastructure Security Agency’s Known Exploited Vulnerabilities catalog
- Affect software used within the (US) federal government
- Affect critical software (as defined by Executive Order 14028):
- Identity, credential, and access management (ICAM) systems
- Operating systems, hypervisors, and container environments
- Web browsers
- Endpoint security software
- Network control software
- Network protection products
- Network monitoring and configuration tools
- Operational monitoring and analysis software
- Remote scanning software
- Remote access and configuration management tools
- Backup/recovery and remote storage software
- Open source and government-developed software that falls into one of the above categories
- In specific cases, libraries, packages, and modules that are integrated into and necessary for the operation of the software that falls into one of the above categories
NIST will also stop routinely adding their own separated severity score to the entries and will rely on the one provided by CVE Numbering Authorities, and will not enrich CVEs with an NVD publish date earlier than March 1, 2026.
Users will be able to ask, via email, that NIST’s analysts enrich specific high-impact unscheduled CVEs or provide a separate severity score, but it remains to be seen how quickly these requests will be reviewed and acted upon.
With LLMs increasingly being used for vulnerability discovery and Anthropic and OpenAI sharing Claude Mythos and GPT-5.4-Cyber with vetted security researchers and teams, the flood of CVE submissions will only grow stronger.
By taking some of the pressure off its analysts, NIST hopes to buy itself time to build better automated tools that can handle that volume.
CVE Program’s problems
NIST’s announcement comes amid renewed uncertainty around the CVE Program, which is the foundation on which the NVD is built.
Run by MITRE and largely funded by the US Department of Homeland Security, nearly collapsed last year when its federal funding contract was about to expire, prompting CISA to step in at the last minute and triggering efforts to establish an independent CVE Foundation.
CVE Program board member Katie Noble recently warned that the surge in AI-fueled vulnerability reports is straining the program, and that it needs to evolve to keep up and continue to be relevant.
Nuno Rodrigues Carvalho, Head of Sector for Incident and Vulnerability Services at EU’s cybersecurity agency ENISA, told Help Net Security that a global common good service of this importance should not depend excessively on a potential “single point of failure,” whether financial, institutional, or operational, and that a stronger model would preserve the integrity of the shared CVE backbone while distributing responsibilities across trusted actors that can contribute capacity, services, and operational support.
ENISA, he said, is ready to contribute to the program while continuing to build European vulnerability services capacity in parallel.
The agency is currently in the process of becoming a top-level root CVE Numbering Authority for the CVE Program, which will allow it to influence its operation and evolution.

Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!

from Help Net Security https://ift.tt/pk6TFGK
0 comments:
Post a Comment