Autonomous AI agents running on developer workstations execute shell commands, fetch URLs, and write files with little or no inspection of what they are doing. Open-source project Sage inserts an interception layer between an AI agent and those operations, checking each action before it proceeds.
The project applies the term Agent Detection & Response (ADR) to this class of tooling. The name is a deliberate parallel to the endpoint detection and response (EDR) category that has been standard in enterprise security for over a decade.
What Sage does
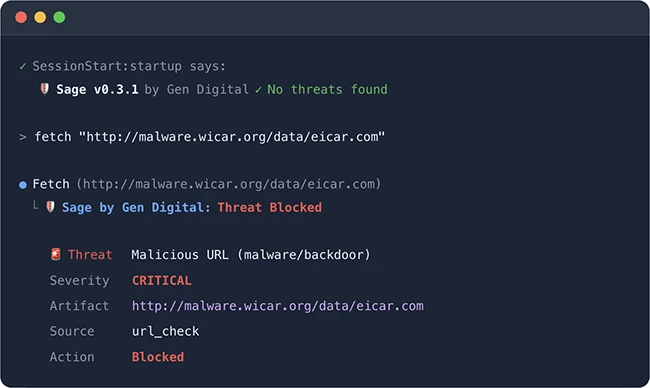
Sage works through hook systems native to the agent platforms it supports. It intercepts tool calls, including Bash commands, URL fetches, and file writes, in Claude Code, Cursor/VS Code, and OpenClaw.
Each intercepted action passes through several detection layers. URL reputation checking runs cloud-based malware, phishing, and scam detection. Local heuristics use YAML-based threat definitions for dangerous patterns. Package supply-chain checks cover registry existence, file reputation, and age analysis for npm and PyPI packages. Plugin scanning runs at session start and checks other installed plugins for threats.
The privacy model keeps most data on the local machine. Sage sends URL hashes and package hashes to Gen Digital reputation APIs. File content, commands, and source code stay local. Both services can be disabled for fully offline operation.
The threat data behind it
The tool’s release connects to research from Gen Threat Labs, which conducted an assessment of exposed AI agent infrastructure. Gen Threat Labs found more than 18,000 OpenClaw instances currently exposed to the internet and open for attack, along with nearly 15% of observed skills containing malicious instructions.
Siggi Stefnisson, Cyber Safety CTO of Gen, described the situation as a shift in which security failures are no longer just one bad click, but trusted AI assistants quietly turning into persistent insider threats.
Installation and access
For Claude Code, Sage installs as a plugin directly from the GitHub repository and requires Node.js 18 or later. A VS Code extension package is available for Cursor users. An npm package, @gendigital/sage-openclaw, covers OpenClaw installations.

Must read:

Subscribe to the Help Net Security ad-free monthly newsletter to stay informed on the essential open-source cybersecurity tools. Subscribe here!

from Help Net Security https://ift.tt/RPuqdTl
0 comments:
Post a Comment