Enterprises are pushing AI deeper into workflows that touch sensitive data across cloud platforms and SaaS apps. The 2026 Thales Data Threat Report, based on a survey of 3,120 respondents in 20 countries, places that shift alongside growing pressure on data protection, identity controls, and cloud security.
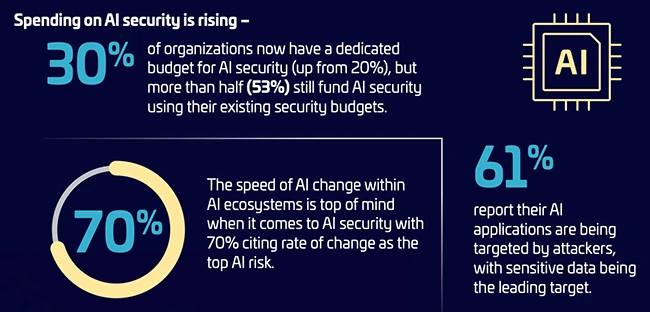
A dedicated budget for AI security is becoming more common. Thirty percent of respondents report having a dedicated AI security budget, up from 20% in the prior year. Many organizations continue to fund AI initiatives through existing security allocations, which keeps AI risk management closely tied to broader cyber programs.
Deepfake activity and AI generated misinformation are now part of routine threat modeling. Fifty nine percent of respondents report experiencing deepfake attacks. Reputational damage linked to AI generated misinformation reaches 48%. These figures sit alongside broader concerns about the security of AI ecosystems and data pipelines that feed models.
Cloud remains a primary attack surface
Cloud assets continue to rank among the most targeted resources. Cloud based storage, cloud delivered applications, and cloud management infrastructure hold the top three positions in reported attack targets at 35%, 34%, and 32% respectively.
The average organization uses 2.26 cloud providers and 89 SaaS applications. That footprint increases the number of identities, interfaces, and data stores that require oversight.
Credential abuse stands out in attacks against cloud management infrastructure. 67% cite credential theft or compromise, including misappropriated secrets, as a leading technique. Third party vulnerabilities and API exposures also register prominently, reinforcing the concentration of risk around identity and access pathways.
Encryption coverage in cloud environments shows uneven adoption. Forty seven percent of sensitive cloud data is encrypted in 2026, down from 51% in 2025. The data reflects gaps in consistent protection across workloads and storage tiers.
Tool sprawl and limited visibility
Data protection programs often span multiple point solutions. 77% report using five or more data protection tools, reflecting broad tool sprawl across environments. That distribution adds friction to policy enforcement and limits consistent telemetry across platforms.
Visibility into data location remains constrained. Only 34% report complete knowledge of where their data is stored. Many organizations continue to track structured and unstructured data across hybrid estates with partial inventories and uneven classification.
Nearly half report using five or more key management systems. Encryption strategies vary between enterprise managed keys and provider managed services, creating mixed control models within the same organization.
Misconfiguration and human error remain the most common causes of data breaches at 28%. Configuration governance and access control discipline continue to influence incident frequency across cloud and SaaS deployments.
Breach reporting differs across leadership tiers. Seventy eight percent of CEOs, presidents, and managing directors report no experience with an on premises breach, compared with 58% across the broader survey population. For cloud breaches, 62% of executives report no prior incident history, compared with 54% overall. The gap reflects differing visibility and reporting perspectives within organizations.
Sovereignty and cryptographic planning
Data sovereignty initiatives continue to influence architecture decisions. Portability is cited by 45% as the primary driver of a sovereignty initiative. Thirty four percent cite a desire for full control over software and data. Workload placement also factors into planning, with 49% indicating that the physical location of cloud infrastructure is important for some or all workloads.
Quantum risk is moving from theory into program planning. Harvest now, decrypt later is cited by 61% as the top quantum-related concern. Fifty nine percent report prototyping and evaluating post quantum cryptographic algorithms. These efforts signal early stage preparation for cryptographic transition in anticipation of future quantum capabilities.
from Help Net Security https://ift.tt/vKqmklf
0 comments:
Post a Comment